Downloading Membership Data CSV
Posted by Titus in Disaster Recovery on September 6, 2017
Due to unfortunate abuse, the Church has generally disabled the ability to download membership data in CSV (Excel) format. Church technical support will tell you that this feature is completely disabled. That’s not quite true. Stake clerks (and ONLY stake clerks) have this ability. Here is how to download Membership data in CSV, after you have received authorization from your Stake President.
1. Log in to LDS.org
Hopefully you know how to do this step.
2. Go to the Directory
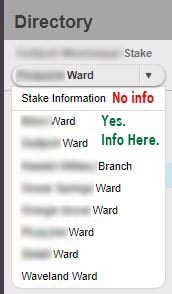
Click Directory, then choose the ward you wish to export, then click the “Export Households” link.

Only Stake Clerks will see the “Export Households” function.
3. You Must Download Each Ward Separately
The church makes it really hard to export data, and you must export each ward individually. Clicking on “Stake Information” will give you no membership data.
If you have 10 units, you will need to do 10 downloads.
4. Yes, I will Use it Only as Directed
I care about privacy a lot (I’m a privacy attorney). I will use the data only as directed, and destroy it after about a month. Someday I’d really like to build a Crisis Caller API so that zero membership data ever leaves church servers, and you view the map through lds.org/maps. But I can’t do that today.
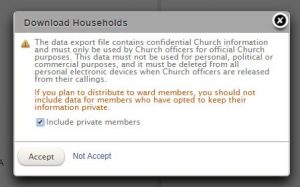
Be sure to get authorization from your Stake President before doing this. Call me at (202) 669-2969 with questions/ concerns.
5. Save the Files. Do not Open.
You will be prompted to either save or open the file. Click “Save” or “Save as…,” depending on your browser. Be sure to save the files in a place you know; do not open them. Warning: The files might automatically download to a default folder, such as your “downloads” folder.
6. Email to aaron [at] crisiscleanup.org
Attach the files to an email, and put the name of the stake in the subject line.
Different Types of Testosterone Boosters in the Market
There are various types available in the market. These options include herbal supplements and prescription medications. Each type has its own unique characteristics and ingredients that can potentially enhance testosterone levels. It’s important to understand these different types to make an informed decision about which one may be suitable for your needs.
Herbal Supplements
One popular type of testosterone booster is herbal supplements timesunion.com. These products are typically made from natural ingredients such as herbs, vitamins, and minerals. They are designed to support the body’s natural production of testosterone. Some common ingredients found in herbal supplements include:
Tribulus Terrestris: This herb has been used for centuries in traditional medicine to improve libido and increase muscle strength.
Fenugreek: Known for its potential ability to boost testosterone levels and improve sexual function.
D-Aspartic Acid: A naturally occurring amino acid that plays a role in regulating testosterone synthesis.
Herbal supplements are often seen as a more natural alternative to prescription medications. They can be easily purchased over-the-counter or online without a doctor’s prescription. However, it’s important to note that the effectiveness of these supplements may vary from person to person.
Prescription Medications
Another option for boosting testosterone is through prescription medications. These medications are typically prescribed by doctors when an individual has low levels of testosterone (a condition known as hypogonadism). Commonly prescribed medications include:
Testosterone Replacement Therapy (TRT): This involves administering synthetic testosterone either through injections, gels, patches, or pellets.
Clomiphene Citrate: This medication stimulates the production of luteinizing hormone (LH), which in turn stimulates the testes to produce more testosterone.
Anastrozole: Sometimes prescribed alongside TRT, this medication helps prevent the conversion of excess testosterone into estrogen.
Prescription medications offer a more targeted approach to increasing testosterone levels. They are usually prescribed after a thorough evaluation of an individual’s hormone levels and overall health. It’s important to consult with a healthcare professional before considering prescription medications, as they may have potential side effects and require regular monitoring.
Varying Effectiveness
It’s important to understand that different types of testosterone boosters may have varying effectiveness based on individual needs. What works for one person may not work for another. Factors such as age, overall health, and lifestyle can influence how well a testosterone booster works.
Some individuals may find herbal supplements to be sufficient in supporting their testosterone levels, while others may require the intervention of prescription medications. It’s crucial to listen to your body and consult with a healthcare professional who can guide you in choosing the right option for you.
Making an Informed Decision
With so many options available, it can be overwhelming to choose the right testosterone booster. However, understanding the different types and their potential benefits is key to making an informed decision. Here are some steps you can take:
Research: Learn about the various types of testosterone boosters available in the market.
Consult with a Healthcare Professional: Seek guidance from a doctor or specialist who can evaluate your specific needs and provide personalized recommendations.
Consider Your Goals: Determine what you hope to achieve by using a testosterone booster – whether it’s increased energy, improved muscle mass, or enhanced libido.
Read Reviews: Look for reviews from other users who have tried different products to get insights into their experiences.
Check Ingredients: Pay attention to the ingredients used in each product and ensure they align with your personal preferences and any allergies or sensitivities you may have.
By taking these steps, you can make an informed decision about which type of testosterone booster is most suitable for you.
Crisis Caller: Example Script
Posted by Titus in Disaster Recovery on September 6, 2017
Running is a popular form of exercise for a reason. It doesn’t need much equipment, and you can do it just about anywhere or anytime it is convenient for you. Plus, experts say it improves heart health.
How Running Improves Your Health
Better cardio health. Running, or jogging, is one of the best cardio exercises you can do. Running for at least 10 minutes a day can significantly lower your risk of cardiovascular disease. Runners lower their chances of dying from heart disease by half.
It also lowers your resting heart rate, the number of times your heart beats per minute when you’re at rest. This is an important indicator of your overall health and fitness. The lower the rate, the more efficient your heartbeat. Check this rolex replica.
.
Better sleep. Quality sleep is essential for your health. Your body repairs itself when you’re asleep, which is why you wake up feeling refreshed. But try to avoid running too late in the day. This can interfere with how well you sleep at night. Aerobic exercise triggers a release of endorphins, chemicals that help relieve pain or stress. These activate the brain and might keep you awake.
Improved knee and back health. A study of 675 marathon runners found that they had a lower arthritis rate than other people. The runners’ knees and backs were both positively affected. The more you run, the lower your odds of back problems as you age.
Improved memory. If you find that you have problems with your memory, get running. It affects your brain in the short and long term. Aerobic exercise gets your heart rate up and makes you sweat. This can boost the size of your hippocampus, the part of the brain responsible for memory and learning.
Fewer colds. If you start to feel a little off, running for 30 minutes can trigger your immune system to help you feel better. When you do aerobic exercises like running at least 5 days a week, you lower your odds of upper tract respiratory infections by 43%.
Better mood and energy. Many people run because they want to feel better. The exercise helps boost your mood, concentration, and overall quality of life. Runner’s high is real.
Setting Running Goals for Success
Having a running goal in mind will help you stay committed. Be sure to set realistic, specific goals that you can measure. If a marathon seems like too much, try a 5K road race. Some tips to help you succeed:
Make a plan, and stay consistent.
Create a routine you can stick to.
Start with a mix of running and walking.
Combine your running program with other forms of exercise for variety.
Run with a friend, or join a local running club.
Talk with your doctor before making a running plan, especially if you have a medical condition or have not exercised in a long time. Your doctor will help you come up with a running program that won’t overstrain your body or mind.
Tips for Healthy Running
For the best results with your running program:
Eat a healthy and balanced diet.
Don’t run right after eating.
Drink plenty of water before, during, and after your run.
Don’t turn your music up too loud. Stay alert and aware of what’s around you.
Wear reflective clothes if running early in the morning or late in the evening.
Tell someone where you plan to run and when you expect to be back.
Avoid isolated and dangerous areas.
Take regular breaks to let your body rest.
If you get an injury while running, stop and get medical care right away.
Posted by Titus in Uncategorized on August 20, 2017
There are several different ways to tell if you are overweight or obese, the quickest of which is a long hard look in the mirror. However, simply looking yourself over is sometimes not enough to tell if you are at increased risk of any health problems because of your weight and even the standard measure of obesity in the UK – body mass index (BMI) – has its flaws. For more dietary tips make sure to visit sandiegomagazine.com/.-
While the BMI measurement has been shown by studies to be a good indicator of an average person’s health risks, the pretty glaring flaw is that the figure used for weight doesn’t take into account what’s fat and what’s muscle. It’s neatly described with the example of a rugby player whose muscle-bound physique means his weight is so high he is defined as obese under the BMI system. Of course a clinical research is always ideal
Then there are the stars of the classic (and it is a classic) film Twins, Arnold Schwarzenegger and Danny DeVito, who would both have BMIs of 34, despite having… somewhat different body shapes.
Body shape is an important factor to consider, because if you have an apple-shaped physique, where fat masses around your midriff, it is considered more dangerous than a pear-shaped body, where fat collects around the hips and thighs.
The apple-shaped bod is more common in men and carrying around that abdominal fat is linked with all sorts of bad news – namely an increased risk of type 2 diabetes, cardiovascular disease and death. That last one sounds particularly bad. Prevent most obesity related conditions after reading these exipure real reviews.
Fortunately, there’s a quick and easy way to tell if you are carrying around too much timber in your midriff, a method that was recently highlighted on the BBC One show The Truth About…, Obesity. As shown in the clip from the show below, all you need for the test is a piece of string.
What You Should Do In Your 20s, 30s, 40s, 50s And 60s To Stay Healthy
The Simple Test That Works Out How Many Carbs You Should Eat
To put into words what was so admirably shown in moving pictures, you grab the string, use it to measure your height, fold that length in half and see if it wraps around your waist. Wrap the halved length of string halfway between your hip bone and your lowest rib. Don’t breathe in – you’ll only be cheating yourself. If the string isn’t long enough to wrap around your entire waist, your waist-to-height ratio (WHtR) is more than 0.5 and you are at increased risk of health problems.
In 2014 researchers from Case Business School looked into the extra risk of early death created by having a WHtR measurement over 0.5 and, pleasingly, they used Twins as an example. They found that, despite their matching BMIs, Arnie (WHtR 0.48) wouldn’t expect to lose any years of life, while DeVito (WHtR of 0.71), risked losing 5.8 years.
Recovery Website
Posted by Titus in Disaster Recovery, Faith on August 26, 2014
At the request of Elder Jeffery Olson, Area Seventy for The Church of Jesus Christ of Latter-day Saints, I recently created a hurricane recovery website for church, which digests disaster recovery principles, tactical guidelines, checklists, and frequently asked questions for stake presidents, bishops, recovery leaders, visiting stakes, and volunteers.
This information was shared with Salt Lake, and will be used as the basis for church-wide disaster preparedness and recovery materials.
I’m looking for volunteers to help translate the material to Spanish and Mandarin.
24 Things Every Midwesterner and Westcoaster Should Know about New Jersey and New York
Welcome to New Jersey and New York. As west coast and Midwest import, I would like to share some of the more pronounced regional differences I’ve learned that will help you understand, appreciate, and love the great land of New Jersey and the 3 1/2 States of New York.
- Unprotected Left-Hand Turns Have the Right-of-Way
- Jughandles
- The Only Rule of the Road: Efficiency
- Public Transportation: It Actually Works
- Real New Yorkers Don’t Have a License
- New Jerseyans Don’t Pump Gas
- Your Town is the Center of the Universe
- Being “From Here”
- No, Really, New Jersey is Beautiful!
- The Statue of Liberty is Actually in New Jersey—Sort of
- There are 3 1/2 States of New York
- “Uptown,” “Midtown,” and “Downtown” are Three Different Places
- It’s the “Shore,” not the “Beach”
- Foodie Heaven
- Conversation is a Sport; Like Jousting
- Treat Sidewalks like Offensive Football
- Jaywalking
- Stand Right, Walk Left
- Role of Government
- Roadside Donations
- Gun Culture
- Tolls
- Parking
- Homes and Other Stuff
Driving and Public Transportation
1. Unprotected Left-Hand Turns Have the Right-of-Way
Every state has its driving quirks. California has “rolling stops,” and Utah has “rolling barricades.” New Jersey has a few driving quirks of its own.
If you are the first car at a stoplight making an unprotected left-hand turn, you have the right of way… at least by custom. Oncoming traffic will wait for you, and if you don’t take the free left, you’re likely to get a honk from the person behind you.
Taking the left turn (quickly, and without hesitation) is considered good driving etiquette because it does not delay oncoming traffic, and speeds the motorists behind you who want to go straight through the intersection. Don’t hesitate—hesitation and trepidation will only confuse other motorists, create a hazard, and earn you glares and honks.
Disclaimer: Either do this right or don’t do it at all. Although I’ve seen cops yield the right-of-way to unprotected left hand turns, I’m pretty sure it isn’t technically legal. If you get T-boned in New Jersey, “I read on a blog post that I had the right of way” is not a valid defense.
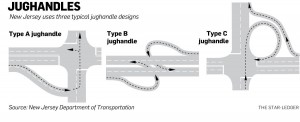
2. Jughandles
New Jersey uses a strange, but efficient intersection configuration called a “jughandle.” Some intersections require you to exit to the right in order to make a left- or U-turn. After you exit to the right, a short strip of road will swing you out to the right, then turn in and intersect the main road at a 90 degree angle. You finish your left-hand turn by going straight through the intersection, or complete the U-turn by turning left.
From above, they can look a little like jug handles.
They’re not so bad once you get used to them. But annoyingly, the jughandle is not uniformly implemented, even on a single stretch of road; so be prepared to make a last-second dart to the right or left to make a left-hand or U-turn. Road signs that say “U Turn,” and point to the right indicate a jughandle.
3. The Only Rule of the Road: Efficiency
Just remember one thing when driving in New Jersey and New York: Efficiency. Whatever you do, be decisive. Imagine every one of your fellow motorists reminding you in a thick New Jersey or New York accent, “Don’t try to be nice, don’t hesitate and don’t slow down. Just do what I think you’re going to do, and we won’t have problems, got it?” A decisive, efficient jerk is safer and tolerated far more than a “thoughtful,” hesitant, or indecisive driver.
In traffic circles, choose the direction you want to go, and just go for it. Others will yield unless they smell fear or indecision. When merging, six inches of clearance is plenty of room. Blink once and merge. If you blink twice, you lose your chance.
I realized how much I have transformed to an efficient east-coast driver when I visited family in Utah. I found myself driving very efficiently, and in the process, cutting off old ladies and probably raising the blood pressure of my fellow motorists. In Utah, that kind of efficiency is inconsiderate. In New Jersey, it’s conscientious because you’re saving yourself and others time.
4. Public Transportation: It Actually Works
Unlike most places in the country, Northern New Jersey and New York have great public transportation. New York’s public transportation is so ubiquitous that most people don’t have a driver’s license (see #5). Taking public transportation is the social norm, and is cheaper than paying tolls and parking (see #22 and #23). Personally, I love the bus and train; my morning and evening commutes are far less stressful than when I have to drive, and I can spend the time writing articles like this.
5. Real New Yorkers Don’t Have a License
In many parts of the United States, getting a driver’s license is a coming-of-age rite of passage. I had my license more or less on my 16th birthday. But in New York City, a driver’s license is irrelevant to most people.
To illustrate, I work in Manhattan. Of my four New York City co-workers, two have never had a license, one let it expire (his exact words were, “I think it expired a year-and-a-half ago,” as if he was talking about an expired library card), and one hardly ever uses his. Licenses are just not relevant. They take the bus, train, subway or cab everywhere. See #4.
6. New Jerseyans Don’t Pump Gas
New Jersey is one of two states in the US that does not allow its citizens to pump their own gas. That’s right… you’re not allowed to pump your own gas. While the official reason for this idiosyncrasy has something to do with protecting the environment, everybody knows that it’s really about jobs.
Important: It is not expected nor customary to tip the person who pumps your gas.
Geography
7. Your Town is the Center of the Universe
Your local community is the center of the universe; remember that, and you’ll integrate fine. I commute to Midtown Manhattan from Northern New Jersey each morning. Having moved most recently from a Maryland suburb of Washington DC, I thought my most recent move was to a New Jersey suburb of Manhattan.
Boy, was I wrong! I quickly found out that Nutley, NJ is most certainly NOT a suburb of Manhattan. A proud town with a distinguished history of its own right, it is more correct to think of Manhattan as a suburb of Nutley, NJ… that is, if you ask anyone from Nutley.
The same could be said for any community in New Jersey or New York. I love the self-contained, community-centric personality of New Jersey and New York communities. In New Jersey, every town has its own school district, stores, mechanics, and miniature financial ecosystem. And anything you could want is no more than a 20-minute drive away.
8. Being “From Here”
Being “From Here” in New Jersey and New York means something very different than in DC, Salt Lake, or California. To illustrate, I can almost literally throw a stone into the adjoining town, Clifton, from my house in Nutley, NJ. I remember once asking a neighbor, “Are you from here?” To which he replied, “Oh, no, no no… I’m not from here. I’m from Clifton.” I encountered similar puzzling responses from people in all areas of New Jersey and New York.
After careful observation, I have determined that if you can drive to your childhood home within 3 minutes, you’re “from here.” Otherwise, you’re from somewhere else.
In general, you are “from” the place you were born and went to high school. If you were born in a different place than you went to high school, then you’re from the place you were born, but you don’t have the same community credentials as someone who was born and raised in that place.
And incidentally, nobody’s from “New York City.” They’re from Queens, or the Bronx, Ryker’s Park, or some other local community (See #11).
9. No, Really, New Jersey is Beautiful!
Before moving to New Jersey, I always thought “The Garden State” was a cluelessly ironic tourist slogan. Poor New Jersey gets picked on for being ugly all the time.
But every New Jersean I know says the same thing, “No really, New Jersey is beautiful!” And now that I live here, I find myself making exactly the same defense. Don’t get me wrong, the I-95 corridor/ NJ Turnpike is, in fact, ugly. But go 10 miles inland, beyond the Meadowlands (what former generations called “swamps”), and you’ll find some of the most picturesque farms, green rolling hills, and postage-stamp towns (my favorite, of course, being Titusville, NJ). New Jersey really is beautiful. No, really… it is!
10. The Statue of Liberty is Actually in New Jersey—Sort of
Take a careful look at the Statue of Liberty in Google Maps, and you’ll notice something peculiar. It’s located inside New Jersey. Yeah, that’s right. The Statue of Liberty is in New Jersey.
At least, that’s what New Jersey thought. New York disagreed, so Congress and the Supreme Court had to step in to settle the matter. Essentially, the Statue of Liberty now sits on a little piece of New York State that sits entirely inside New Jersey. But just because the Supreme Court made a decision doesn’t mean every New Jersean is convinced.
New Jerseans also like to point out that the New York Jets and Giants play in New Jersey, and Super Bowl XLVIII was in New Jersey, among other facts.
11. There are 3 1/2 States of New York
Let’s start with a Google Earth view of the New York/New Jersey area, to the right (click to enlarge). You’ll see New York (to the North) and the large chunk of land completely surrounded by water, called “Long Island” by geographers. And although you might assume that everything to the west is New Jersey, it’s not. The section marked “Not New Jersey” is Staten Island, and even though its geography appears to be connected with New Jersey, it is most certainly NOT part of New Jersey.
Now that we’ve identified land masses, it’s time to talk about the real New York, or rather, the 3 1/2 States of New York:
- 1. The State of Upstate New York
- 2. The State of The Five Boroughs (A.K.A. “New York City”)
- 3. The State of Long Island (As differentiated from the geographic feature with the same name)
- 3 1/2. The half-State of Staten Island (Technically one of the Five Boroughs)
Upstate New York is, in the mind of most people in the Boroughs, a pretty, but mostly irrelevant land mass to the north. Upstate and the other New Yorks don’t have much in common, and they don’t talk to one another too much. Occasionally they’re forced to interact when people in Albany (the state capitol of the State of Upstate New York) try to interfere with policies of The State of New York City.
To add some nuance: The people of Upstate New York use the phrase “Downstate New York” to describe everything within about 85 miles of New York City, including Putnam, Dutchess, and Orange Counties. But nobody in the Boroughs or Long Island consider themselves “Downstate.” Many have never heard the term, or would find it insulting. In contrast, the people of New York City and south refer to everything north of Westchester as “Upstate.” As a result, poor Putnam, Dutchess, and Orange counties feel disowned by both Upstate New York, and New York City.
The Five Boroughs include Manhattan, Brooklyn, the Bronx, Queens, and Staten Island. Together, they comprise “New York City,” although almost nobody from the five Boroughs refers to “New York City.” Most people refer to the Borough they’re from, and only use “New York City” when talking to out-of-staters. Tourists who lack an appreciation for New York’s size often think of Manhattan (or more particularly Times Square) as “New York City,” but this is a misperception. Two of the Burroughs, Brooklyn and Queens, are technically located on what geography majors would call “Long Island,” but I assure you, the Five Boroughs are most certainly NOT on the real Long Island.
To add some nuance: Due to its convenient location, many Brooklynites and other natives of the Boroughs have moved to Hudson County, New Jersey, just across the River. Consequently, some in New York City refer to Hudson County as “The Sixth Borough,” but not too loudly while they’re actually in New Jersey. Such a suggestion would deeply offend New Jersey’s sense of sovereignty and identity (See #10).
Long Island begins where Queens ends, and not an inch before. It has a distinct identity, culture, and needs from the other 2 1/2 New York States, and due to its relative remoteness, Long Island behaves like a separate state in most practical respects.
Staten Island. I’ll be the first to admit that I do not understand Staten Island’s complicated relationship with the other four boroughs, but I’d have to designate Staten Island as another half-state: It is separate from New York City; it has nothing to do with Long Island; less to do with Upstate New York; and has absolutely nothing in common with New Jersey except I-278.
And it’s worth mentioning that the Hudson River might as well be an ocean, because the land masses on either sides are completely different countries.
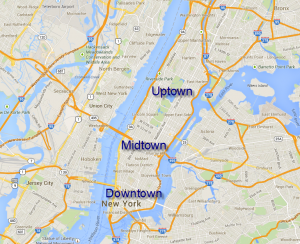
11. “Uptown,” “Midtown,” and “Downtown” are Three Different Places
Many cities in the West and Midwest refer to their city center as “downtown.” When someone says, “I’m going downtown,” it’s more or less synonymous with “I’m going into the city.”
But not so in Manhattan. Within a several-hundred-mile radius of Manhattan, “Downtown,” “Midtown,” and “Uptown” refer to very particular sections of Manhattan. The best I can tell, Downtown goes from the southern tip of Manhattan to somewhere between 14th and 30th street, and includes the financial district. Midtown stretches from there to about 59th street, and includes Times Square and the southern edge of Central Park. And Uptown extends from there, north.
To illustrate, the following conversation would confuse anyone in this area: “I’m going downtown,” you say. “Oh, where to?” asks a native. “57th Street,” you reply. The native gives you a puzzled look because 57th Street is Midtown, not Downtown.
It is permissible to use “Downtown” when referring to another city, but you must indicate the city, e.g. “I’m going to downtown Newark.” But if you say, “I’m going Downtown,” it means you’re going to Manhattan, south of about 30th street. And there is no such thing as “Midtown” or “Uptown” in any other city. Those two places belong exclusively to Manhattan.
13. It’s the “Shore,” not the “Beach”
In New Jersey, never refer to the “beach.” All of the sunny places with sand and ocean are called the “shore.”
Same goes for New York…unless you’re going to The Hamptons. Then it’s not the beach, or the shore… it’s called “going to The Hamptons.”
Friendliness and Interacting with Others
14. Foodie Heaven
New York and New Jersey are Foodie Heaven. You could eat at a new restaurant every meal for years and never scratch the surface of good eateries. Unfortunately, I’m not a foodie.
15. Conversation is a Sport; Like Jousting
Every town and borough has a unique personality, but to Westerners and Midwesterners, people from all over this area seem somewhat abrasive and unfriendly. I assure you that people actually are quite friendly and open.
When you encounter someone who seems abrasive, just remember that they’re trying to be direct and efficient, and will appreciate the same in return. Think of conversation as a competitive sport—like jousting—where everyone is a good sport and each respects a worthy opponent. Once you understand that, you’ll grow to appreciate that directness is a form of friendliness.
16. Treat Sidewalks like Offensive Football
If you ever take a trip to Manhattan, you will find the sidewalks packed with people. If you find yourself bumping into people, use this one simple trick: Avoid looking at people, and instead look directly where you want to go. Pretend like you’re a halfback: Find your hole, then head directly for it. Looking the direction you are going will cue oncoming pedestrians, and they will walk the other way. But if you start looking at people, they can’t tell which way you’re going, so you end up bumping into one another or doing a sidewalk dance.
17. Jaywalking
Like the road, the only rule you need to remember about being a pedestrian is efficiency (See #3 above). Jaywalking is pretty much essential if you want to arrive on time and not slow down your fellow pedestrians. Jaywalking doesn’t mean you should be stupid and unsafe; after all, it is very inefficient to be hit by a car, so be sure to avoid that.
18. Stand Right, Walk Left
On escalators, stand to the right to let others pass on the left. As a tourist, you may want to take your time and drink in every moment, but right behind you is a cranky commuter who just wants to get home and see her family, no matter the time of day or night.
Laws and Government
19. Role of Government
Without using the words “Conservative” or “Liberal,” taxes are generally higher out here, and there is a stronger acceptance that the government has a greater responsibility to take care of residents. The ethic of self-sufficiency is not as strong in urban areas, compared with the Midwest and West Coast.
Also, there is more of a general acceptance that you must ask permission from the government to do most things. Whether a permit is required, most of my neighbors would ask if they needed a permit to have a garage sale, paint their house, have a really big party, or help a neighbor muck out after a hurricane. You get the idea.
20. Roadside Donations
Ironically, though you need a permit to have a garage sale, it is socially acceptable to leave unwanted items or valuable scrap (not trash) on the side of the road as a way to get rid of them. This whole area uses the curb instead of Craigslist. Regardless of the neighborhood, it is socially acceptable to stop in front of strangers’ houses and pick through belongings in their front yard. Nicer neighborhoods have nicer furniture on their curbs, and our house is furnished with items found on the side of the road.
Instead of taking a broken washing machine to the dump, we put it on the curb. Within 7 minutes (this is not an exaggeration), it had been picked up for scrap. We recently had a garage sale (which required a permit), and sold about 25% of our inventory. We left the unsold items on the front lawn for 36 hours, and were able to get rid of almost 80%.
21. Gun Culture
There isn’t one.
Most people can’t imagine why anyone who isn’t a criminal or police officer would ever want to own a gun. They’re pretty highly regulated, and handguns are outright banned in New York City.
Cost of Living
22. Tolls
There are tolls. Everywhere. I drive to Queens about twice a month, and my toll bill averages $60/month. Going over a bridge or tunnel will run you around $13 in the city, and around $5 elsewhere. Most people (including myself, against my own privacy instincts) have EZ Pass, which automatically deducts the amount from a credit card.
I recently realized how accustomed to paying tolls I had become when I drove to Pittsburgh. I traveled through several tunnels, and each time I found myself thinking, “Wow! Another FREE tunnel! This is awesome!”
23. Parking
As of the date of this post, parking in the city will run you $25-$45 for a couple of hours. $18 for an hour or two is a great deal.
24. Homes and Other Stuff
It should come as no surprise that homes, property taxes, and most other stuff is just more expensive. But plenty of regular non-millionaires still live out here, so it’s possible to make a living.
You can get a house, just not as much. When I visited my sister’s relatively capacious house in Southern Utah, I asked her whether she was paying $6,000 per month for the house. She was paying about $650.
Conclusion
Whether you’re a Westerner moving to the East Coast, a tourist, or a native who appreciates an outside perspective, I hope this blog post helps you appreciate and acclimate to the great lands of New Jersey and New York.
Did I miss something? Do you have a tip of your own? Let me know in the comments below.
Update 6/8/2014: Added gun culture, curbside donations, and some more details.
Update 6/15/2014: Added pumping gas.
Essential Marketing Blogs and Podcasts to Follow
In the fast-evolving world of marketing, staying up-to-date with the latest trends, tools, and strategies is essential for success and have the insight of experts like Marketing Heaven. Following the right blogs and podcasts can provide valuable insights, practical advice, and inspiration from top industry experts. Whether you’re a seasoned marketer or new to the field, these resources offer an excellent way to keep learning and stay ahead of the curve.
Here’s a list of some essential marketing blogs and podcasts that cover everything from content marketing and social media strategies to SEO and digital analytics.
Top Marketing Blogs to Follow
1. HubSpot Blog
Focus: Inbound marketing, sales, and customer service
Why Follow: HubSpot is a pioneer in inbound marketing, and its blog is a go-to resource for comprehensive guides on content marketing, SEO, email campaigns, and social media. The blog regularly covers actionable insights and strategies for building customer relationships, boosting sales, and using HubSpot’s own tools.
2. Neil Patel Blog
Focus: SEO, content marketing, and social media
Why Follow: Neil Patel, co-founder of companies like Crazy Egg and Hello Bar, is a leading voice in digital marketing. His blog is packed with expert advice on SEO and content strategies, and he frequently publishes updates on Google’s algorithm changes and other developments in digital marketing.
3. Moz Blog
Focus: SEO, digital analytics, and content strategy
Why Follow: Moz is renowned for its expertise in SEO, and its blog provides in-depth articles, guides, and case studies to help marketers navigate the intricacies of search engine optimization. Moz’s “Whiteboard Friday” series is especially popular for its clear and concise explanations of SEO topics.
4. Content Marketing Institute (CMI) Blog
Focus: Content marketing, storytelling, and audience engagement
Why Follow: CMI’s blog is dedicated entirely to content marketing, covering everything from creating a content strategy to measuring ROI. It’s an excellent resource for learning how to use content to engage audiences, build brand loyalty, and drive conversions.
5. Social Media Examiner
Focus: Social media marketing and digital engagement
Why Follow: Social Media Examiner is one of the most comprehensive resources for social media marketing. The blog provides expert tips and tactics for platforms like Facebook, Instagram, LinkedIn, and YouTube. It also features news on social media updates and tools to keep marketers in the know.
6. Copyblogger
Focus: Copywriting, content creation, and digital marketing
Why Follow: Copyblogger is perfect for marketers interested in improving their content and copywriting skills. The blog covers the essentials of persuasive writing, storytelling, and creating high-impact content that drives engagement and conversions.
7. Ahrefs Blog
Focus: SEO, link building, and content marketing
Why Follow: Known for its powerful SEO tools, Ahrefs also runs an insightful blog that offers tutorials and strategies for improving search visibility, mastering keyword research, and building a solid backlink profile.
8. MarketingProfs
Focus: Marketing education, research, and career development
Why Follow: MarketingProfs offers a mix of practical advice, industry research, and trend analyses, making it a valuable resource for professional development in marketing. Their blog covers a wide range of topics, from lead generation to marketing leadership.
Top Marketing Podcasts to Follow
1. Marketing Over Coffee
Hosts: John Wall and Christopher Penn
Focus: Digital marketing, social media, and analytics
Why Listen: Recorded weekly from a coffee shop, this podcast provides a casual yet informative look at digital marketing trends and tools. The hosts discuss everything from AI in marketing to the latest SEO tactics.
2. The Smart Passive Income Podcast with Pat Flynn
Host: Pat Flynn
Focus: Entrepreneurship, online business, and marketing
Why Listen: This podcast is geared towards marketers and entrepreneurs looking to build and monetize online businesses. Pat Flynn shares his personal insights and brings on industry experts to discuss tactics for content creation, digital advertising, and audience growth.
3. Call to Action by Unbounce
Host: Unbounce team
Focus: Landing pages, conversion optimization, and digital campaigns
Why Listen: Call to Action dives into the science of conversion rate optimization and how to create landing pages that convert. The podcast is packed with case studies and advice on creating high-performing campaigns.
4. The GaryVee Audio Experience
Host: Gary Vaynerchuk
Focus: Social media, branding, and entrepreneurship
Why Listen: Known for his direct style, Gary Vaynerchuk’s podcast covers a range of topics, from leveraging social media for brand building to entrepreneurial mindset. It’s a great listen for anyone looking for motivation and fresh ideas in marketing.
5. Online Marketing Made Easy with Amy Porterfield
Host: Amy Porterfield
Focus: Digital marketing, online courses, and email marketing
Why Listen: This podcast is ideal for small business owners and marketers looking to grow their online presence. Amy Porterfield shares actionable strategies for launching digital products, building email lists, and creating content that resonates with audiences.
6. Perpetual Traffic
Hosts: Ralph Burns and Kasim Aslam
Focus: Paid traffic, social media ads, and conversion optimization
Why Listen: This podcast focuses on strategies for driving traffic and conversions through paid advertising, primarily on platforms like Facebook and Google. It’s a valuable resource for those interested in paid media and lead generation.
7. Duct Tape Marketing
Host: John Jantsch
Focus: Small business marketing, brand building, and strategy
Why Listen: This podcast offers practical advice for small business owners, with episodes covering a range of marketing topics, including brand building, content marketing, and referral strategies.
8. Marketing School with Neil Patel and Eric Siu
Hosts: Neil Patel and Eric Siu
Focus: Digital marketing tips, SEO, and content strategies
Why Listen: Neil Patel and Eric Siu keep their episodes short and impactful, offering daily insights into different aspects of digital marketing. It’s perfect for busy professionals who want bite-sized advice.
9. The Content Strategy Podcast
Host: Kristina Halvorson
Focus: Content strategy and planning
Why Listen: Kristina Halvorson dives deep into content strategy, bringing on industry experts to discuss best practices for creating, managing, and scaling content in a way that supports business goals.
10. The CMO Podcast
Host: Jim Stengel
Focus: Marketing leadership and brand building
Why Listen: Jim Stengel, former CMO of Procter & Gamble, interviews top marketing executives from leading brands. The podcast offers a behind-the-scenes look at the strategies that drive successful marketing campaigns and brand leadership.
Why Following Marketing Blogs and Podcasts Matters
Staying updated on the latest trends and tactics is crucial in the marketing field, where best practices change frequently with new technologies and platforms. Blogs provide in-depth articles, case studies, and how-tos, which can serve as useful references for implementing new strategies. Podcasts, on the other hand, offer the convenience of learning on-the-go and often feature candid conversations with industry experts who share their real-world experiences and insights.
By following the blogs and podcasts mentioned here, you’ll be better equipped to stay current, refine your skills, and bring new ideas to your marketing strategy. These resources can also spark creativity, challenge assumptions, and help you anticipate shifts in the marketing landscape.
Conclusion
Whether you’re looking to deepen your understanding of SEO, improve your content marketing skills, or explore new social media strategies, these blogs and podcasts are excellent resources for any marketer. Following a mix of both will ensure you’re well-informed and equipped to navigate the ever-evolving world of marketing with confidence.
The Paradox of non-Profit Innovation
Posted by Titus in Disaster Recovery on June 26, 2013
Cross-posted here.
Are we there yet?
As Project Manager for Crisis Cleanup, the most frequently asked questions I receive are, “When will it be done?” or “How much money do you need to finish Crisis Cleanup?” A variation on this is, “Well, it works, right? Why do you need more money if it works?”
That’s the problem with innovating (especially non-profit innovation). If you simply explain the idea, nobody takes you seriously. You just have to execute and show everybody a “finished” product. Only then do they see how amazing your idea was. But then you’re in a catch-22. After all, if you built your idea without any help, why do you need help to keep going?
I feel a bit like I just built the Model-T Ford in a world of horse and buggies. Most people could not have conceived of the automobile until they saw it for the first time. Everyone is amazed at the technological marvel, and it is received gratefully and with congratulations. But they don’t understand that they really need an airplane or a rocket. I’m trying to build a rocket, not a Model-T Ford. But to people who are still figuring out how to dismount their horse and use a clutch, a rocket is inconceivable.
Thus, the paradox of innovation continues: Lack of vision and inertia perpetuates inefficiency, which stifles vision.
Quit Whining and Get some Funding
I am do-gooder number 14,000,001 who has thought, “all I need is some funding, and I can really change the world.” Sigh.
In a free market, for-profit ventures can attract funding and resources once you write a compelling business plan. There is at least one consistent pattern to all business plans: You create value for customers, and extract value from those customers—making a profit in the process.
But free markets don’t do very well at helping victims or survivors. First, you can’t treat victms as customers, because extracting value directly from victims (e.g. victims of natural disasters, victims of identity theft, victims of crime, etc.) is unseemly, unethical, or illegal. As a result, interested third parties such as the government or philanthropic organizations must provide the value on behalf of the victims and survivors. But because we live in a liberty-preserving society, these interested third parties are not permitted to make a profit off victims, with the possible exception of lending institutions.
Principles of insurance and market pressures dictate that victims are restored to the minimum degree necessary to prevent (costly) social disorder. Under no circumstance are they, or the people who help them, ever made completely whole or come out ahead.
This reality stands in contrast to the business world, where I can negotiate a high salary if I can make the business even more. But natural downward pressures on do-gooders’ salaries means that nobody (honest) gets rich from just helping victims. As a result, most people who help survivors aren’t driven by money (which is OK with me, because it means that the disaster recovery community is filled with some of the best people on earth).
Tilting Against Windmills
I’ve learned that competing for grant money is a bloodsport. I’m not saying that a grant is impossible, I’m just saying that for me, holding down a full-time job, raising a family (number 6 will arrive in September), church service, while managing the development and deployment of Crisis Cleanup is enough to keep me occupied without tilting against grant-writing windmills as well. I was turned down by the Robin Hood Foundation; dealing with the American Red Cross was perhaps the most Kafkaesque experience of my life, and I have yet to hear a peep from the Knight Foundation.
And that brings me back to the paradox of innovation. Poor vision and inertia perpetuates inefficiency. Unfortunately, most grant-writing organizations aren’t exactly known as bastions of innovative vision. I hope there are some out there, among all of those windmills.
So, if somebody finds a cutting-edge innovative government agency or philanthropic organization with extra grant money that will pay more than they have to on behalf of survivors (now that’s a compound oxymoron if I’ve ever seen one), let me know. In the meantime, I’ll be in my basement tinkering with rocket parts.
Bitcasa Review: Version 1.1.0.0
Posted by Titus in Reviews, Technology on May 30, 2013
Running is a popular form of exercise for a reason. It doesn’t need much equipment, and you can do it just about anywhere or anytime it is convenient for you. Plus, experts say it improves heart health.
How Running Improves Your Health
Better cardio health. Running, or jogging, is one of the best cardio exercises you can do. Running for at least 10 minutes a day can significantly lower your risk of cardiovascular disease. Runners lower their chances of dying from heart disease by half.
It also lowers your resting heart rate, the number of times your heart beats per minute when you’re at rest. This is an important indicator of your overall health and fitness. The lower the rate, the more efficient your heartbeat. These are the best diet pills.
Better sleep. Quality sleep is essential for your health. Your body repairs itself when you’re asleep, which is why you wake up feeling refreshed. But try to avoid running too late in the day. This can interfere with how well you sleep at night. Aerobic exercise triggers a release of endorphins, chemicals that help relieve pain or stress. These activate the brain and might keep you awake.-
Improved knee and back health. A study of 675 marathon runners found that they had a lower arthritis rate than other people. The runners’ knees and backs were both positively affected. The more you run, the lower your odds of back problems as you age.
Improved memory. If you find that you have problems with your memory, get running. It affects your brain in the short and long term. Aerobic exercise gets your heart rate up and makes you sweat. This can boost the size of your hippocampus, the part of the brain responsible for memory and learning. Read more about nootropics.
Fewer colds. If you start to feel a little off, running for 30 minutes can trigger your immune system to help you feel better. When you do aerobic exercises like running at least 5 days a week, you lower your odds of upper tract respiratory infections by 43%.
Better mood and energy. Many people run because they want to feel better. The exercise helps boost your mood, concentration, and overall quality of life. Runner’s high is real.
Setting Running Goals for Success
Having a running goal in mind will help you stay committed. Be sure to set realistic, specific goals that you can measure. If a marathon seems like too much, try a 5K road race. Some tips to help you succeed:
Make a plan, and stay consistent.
Create a routine you can stick to.
Start with a mix of running and walking.
Combine your running program with other forms of exercise for variety.
Run with a friend, or join a local running club.
Talk with your doctor before making a running plan, especially if you have a medical condition or have not exercised in a long time. Your doctor will help you come up with a running program that won’t overstrain your body or mind.
Tips for Healthy Running
For the best results with your running program:
Eat a healthy and balanced diet.
Don’t run right after eating.
Drink plenty of water before, during, and after your run.
Don’t turn your music up too loud. Stay alert and aware of what’s around you.
Wear reflective clothes if running early in the morning or late in the evening.
Tell someone where you plan to run and when you expect to be back.
Avoid isolated and dangerous areas.
Take regular breaks to let your body rest.
If you get an injury while running, stop and get medical care right away.
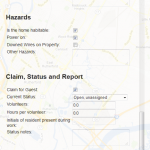
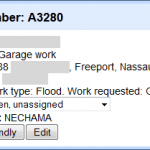
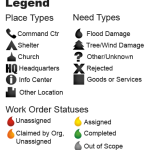
Disaster Recovery Collaborative Work Order System
Posted by Titus in Disaster Recovery on December 20, 2012
Update 24 Mar 2013: I have Finally launched the Official Crisis Cleanup Blog, including a more up-to-date version of this post.
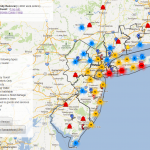
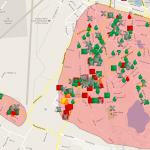
Over the past several months a few developers and I have created a Collaborative Work Order System for disaster recovery (now at CrisisCleanup.org, Twitter: @CrisisCleanup). The project is open source under the Apache 2.0 License, and is a gift to the community. The system is now being used to manage recovery efforts in Connecticut, New York, New Jersey, Mississippi, and Georgia. The National VOAD will formally adopt/assume the project in May at the National VOAD conference. Many thanks to the dedicated work of Andy Gimma, Jeremy Pack, Chris Wood and dozens of others who have made this volunteer effort more successful than I could have ever imagined at the outset.
The platform implements a �Craigslist� philosophy to recovery efforts�organizations that are aware of work orders enter them into the system, and organizations with capacity to help can claim and perform the work without interference from any centralized organization. This minimizes duplication and maximizes communication, coordination, and efficiency.
No single organization can guarantee that any of the individuals in the system will be served. However, using the same system will permit inter-agency coordination, situational awareness, and help participating organizations prioritize their limited resources. And sharing work order information among dozens of organizations maximizes the chances that a client will receive help.
As of right now, more than 90 relief organizations and agencies with more than 30,000 combined volunteers are using the system to coordinate Hurricane Sandy relief efforts. The system is managing more than 4,900 homes in need of gutting and rebuilding from Connecticut, Long Island, New York, New Jersey, Mississippi and Georgia.
There are three requirements for an organization to participate in the system:
- An organization must have a physical presence in the disaster area.
- An organization must either perform home assessments and/or perform gutting, mucking-out, debris removal, mold abatement, or rebuilding.
- An organization must be reputable. This generally means that the organization must be non-profit, or a member of National VOAD, a state VOAD, a County VOAD/COAD, a local government agency, or come recommended by a VOAD member or government agency.
The current implementation requires a password. However, I have posted a training video that explains how the system works. I’ve also included screenshots below.
Philosophy Behind and Limits to the Collaborative Work Order System
The system is based upon a few foundational philosophies:
- Retired Admiral Thad Allen observed that in the military, they operate under a “Unity of Command,” but in private sector disaster recovery, the best you can hope for us “Unity of Effort.” This tool facilitates Unity of Effort without striving for the mirage of private sector Unity of Command.
- I don’t want to be in charge of your organization’s activities, or tell you what to do.
- The system should enable, not interfere with your existing business processes.
- No single organization should be in charge of others without their consent.
- The system should make collaboration and communication not only convenient, but required.
- This is not the “One App to Rule them All.” Do not stray too far from the system’s strengths.
- The system is open (but not public), and should therefore not contain sensitive personal information.
App Development Philosophy
There are two approaches to app development. The first is to create a mammoth, fully-integrated system that tries to be all things to all people. Sahana is a great example of this approach. However, even the most successful of these apps can be overwhelming and tend to be a jack of all trades but master of none.
The second approach is to try and create a relatively lightweight app that does only one thing very well. These apps are generally far more user-friendly; but their success comes with a cost. Without careful curation, these apps can be highjacked, forced to do things outside their core competency, and grow into unwieldy mammoths.
The Collaborative Work Order System definitely falls into category 2. There is no such thing as “The One App to Rule Them All,” and this is no exception. The Collaborative Work Order System excels at coordinating tens or hundreds of thousands of volunteers from multiple organizations, to thousands or tens of thousands of work order sites across a large geographic area; improving communication, and improving inter-organization coordination. But there are certain things for which it should never be used.
For example, because the system is open (but not public—there is an important difference), it is inappropriate to use the system to store sensitive personal information. The system’s power to coordinate and facilitate communication comes from its openness; but some things were not meant to be shared, such as confidential case management information, volunteer details, etc. The Collaborative Work Order System is not, and can never be, all things to all people. The Collaborative Work Order System should never be used to store sensitive personal or case management information.
Why a Collaborative Work Order System Hasn’t Been Developed Before
In the disaster recovery community, we talk a good deal about VOAD’s 4Cs: Cooperation, Communication, Coordination, and Collaboration. One reason these ideals are so difficult to achieve is because, even though we don’t like to admit it, most disaster recovery organizations are essentially competitors. Of course, we all get along in the field, forging deep and lasting friendships while we labor side-by-side in the service of our fellows in distress. But almost all relief organizations (with exceptions like Mormon Helping Hands and Occupy Sandy) rely upon grants to fund their operations.
Passive competition for scarce grant resources means that every organization wants to be in charge. In an effort to qualify for the next grant, each organization strives to direct the work of other organizations and, most importantly, each organization wants to control the flow of information. These tensions create natural barriers to the 4Cs.
In addition, organizations with employees have a tendency to perpetuate inefficiency. Even though efficiency saves the organization money, efficiency may also eliminate jobs. Therefore, most bureaucracies are suspicious of or downright hostile towards new or efficient technologies.
In short, a collaborative work order system hasn’t been developed until now because: 1. Everybody wants to be in charge; and 2. Internal bureaucratic interests run counter to efficiency.
My Unique Opportunity
First, allow me to start with a disclaimer: The Collaborative Work Order System is neither developed nor formally endorsed by The Church of Jesus Christ of Latter-day Saints/ Mormon Helping Hands, and this blog post represents my own opinion and not the official position of the Church. In my role as New Jersey VOAD representative for the Church, I have had a wonderful opportunity to tackle these difficult problems during Hurricane Irene, the June 2012 derecho storms, and Hurricane Sandy. First, because Mormon Helping Hands relief efforts do not rely on government grants, it has no economic incentive to be “in charge” of other organizations. We just want to help everyone get the job done.
As a result, I designed the system so that no single organization is capable of controlling the information or governing other organizations without consent. The technology permits, but does not require oversight. Who is in charge? The answer to that question is the same as this question: “Who is in charge of Craigslist?”
This non-threatening approach is designed to facilitate an organization’s existing business processes, rather than impose new processes. As Joseph Smith taught, people can “govern themselves” when they operate according to correct principles. And based upon the participation of more than 90 organizations, the approach works.
Second, unlike most other relief organizations, Mormon Helping Hands relies exclusively on volunteers with families and full-time jobs. Unlike employees, volunteers have a natural inclination to work efficiently, and are therefore more open to adopting disruptive or efficient technologies. Mormon Helping Hands volunteers (as well as Occupy volunteers) don’t get paid, and if they’re anything like me, they must hold down a full-time job make time to see their wife and five cute kids. Volunteering efficiently improves my personal bottom line.
Real Innovation
The Collaborative Work Order System’s technology is not new or particularly innovative. Due to the great work of developers like Jeremy Pack, the user interface is great, but not groundbreaking. In fact, if I leave you with the impression that the Collaborative Work Order System is just a cool technology, then I have failed. This system does not evangelize technology; it evangelizes a philosophy.
The real innovation of this system is the ability to coordinate tens of thousands of volunteers from dozens of organizations to thousands of sites after a disaster. The Collaborative Work Order System proves that it is possible to create a near frictionless technological platform where inter-organization Cooperation, Communication, Coordination, and Collaboration is not only convenient, but required.
Next Steps for Development
Since launching CrisisCleanup.org, the mostly volunter-driven project has received a lot of attention from FEMA, and VOADs across the country. If all goes well, I intend to give long-term stewardship of the project to National VOAD, which will be in a better position to evangelize and maintain the project long-term.
In the meantime, we’re working on some big upgrades. Well, they won’t look big to end users, but they require some heavy lifting in the database. Here is a current list of development priorities:
- Create a new Incident on the fly
- Streamline joining CrisisCleanup.org, and allow organizations across the country to join during peacetime.
- Adapt the tool for Long-Term Recovery (LTR) including Rebuilding and Refurbishing.
- Import Work Orders
- Public-facing, de-identified and blurred map
- Duplicate work order detection and merging
- Fully-functional administrative back-end
- Create a Mobile interface
- Manage Spontaneous Unaffiliated Volunteers (SUVs) and connect SUVs with volunteer organizations
- Enable a separate “Canvassing” map that will allow others to see which areas have been canvassed, and which have been ignored
- Send Text Messages to Team Leaders with Work Order Information
- More easily contact other organizations in the field
- Scope of Project: The system is primarily focused on the assessment, gutting, and rebuilding phases of recovery. It does NOT handle case management, inventory control, or volunteer management, etc. However, it will track volunteer hours.
- Can the system be adapted outside of the New York/ New Jersey area? Yes. The system is geographically agnostic.
- How much does the system cost? I don�t charge (and don�t plan on charging) organizations to use the system. In addition, the code is free to download, adapt, and install. It is open source, provided under the Apache 2.0 license, and was created by volunteers. Although the code is free, hosting and programming is not. Hosting costs vary from $50-$200 per month, depending upon usage. Ongoing programming support will also require funding. Right now a generous volunteer is paying for the hosting out of his own pocket, and volunteer programmers have created the system. I will probably need a long-term funding source.
- Have you considered crowdsourced funding? Yes, I’ve considered everything, including crowdsourced funding. But I only have so many hours in each day, and when I’m not cleaning up a hurricane or being a dad, I have a pesky full-time job to maintain. If you’d like to help get funding, drop me a line.
- Can I install a version for myself? Yes, but I wouldn�t recommend that right now. You�ll need your own developer, and because the system is being improved, you�ll have to manually install all new patches as they come out. Instead, the system will be designed to handle any number of new incidents as they arise. You will be able to create a new incident in the existing system, any time.
- What if a disaster happened tomorrow in my state? Could we use this system? Short answer: Yes. Long answer: Right now it will take 6-12 hours to set up a new incident in the system. We�re making programming improvements that should turn around that time to near zero.
- What are the long-term plans for the system? The code will always be open source and available to anyone who wants it. I hope to be able to offer the service for free to any voluntary organization who needs to use it, also. But I�m making this up as I go along, and I feel like I�ve been constructing an airplane while in free-fall, writing the owner�s manual and giving status updates for the past 2 1/2 months.
- Will the system do case management? No. Because of the open nature of the system, it is not appropriate to store or track confidential case management information using this system. The system is primarily focused on the assessment, gutting, cleanup, and rebuilding phases of recovery. It does NOT handle case management, inventory control, volunteer management, etc. However, it will track volunteer hours.
- Will the system adapt for long term recovery? Yes, with limits. We are adapting the system to do long term recovery for property, but not other aspects of LTR, such as case management.
- What does the system do best? The system is designed to organize and coordinate tens or hundreds of thousands of volunteers from multiple organizations, to thousands or tens of thousands of work order sites across a large geographic area; improve communication, and improve inter-organization coordination. It has been successfully used to deploy more than 30,000 volunteers during Hurricane Sandy, and manage more than 4,600 work order sites.
- Will this system manage Spontaneous Unaffiliated Volunteers (SUVs)? No, not really. Because the system includes location and contact information for clients, it would not be prudent to allow the entire public to access the system. Consequently, SUVs must first affiliate with an organization before using the system.
- This system is great! Can you make it do something else?: Yes! If you give me a programmer (or a grant), it will be done tomorrow. Until then, the answer is probably “not for a while,” but there is probably a workaround that will get the job done for now.
- Bugs: We’ll fix bugs as volunteer programmers have time.
- How do I�? I cannot provide technical support. I have found that the training video answers 95% of questions. Please watch it. If you figure out how to do something, chances are someone else would like to hear about it. PLEASE email me your how-to, and I will include it in the knowledge base.
- Will you give me a report? No. I’ll probably give you a username and password and let you pull your own reports.
- Information for Programmers: The source code is released under a Apache 2.0 License. Here is a list of open issues. Please grab a bug, submit a patch, and start working!
- Programmer Skill Set: Python, Javascript, with Google Maps familiarity. Familiarity with appspot.com is beneficial. I also need help developing the database schema, and laying a good foundation for others to build upon.
As you can see, we have a long list of high priorities. We’re making slow progress, but hopefully we’ll be able to get some funding to continue development.
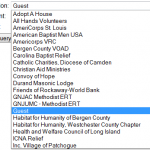
Participating Organizations
The following organizations are or have participated in the Collaborative Work Order System:
| Adopt A House | MHH-Philadelphia PA Stake |
| All Hands Volunteers | MHH-Plainview NY Stake |
| American Baptist Men USA | MHH-Queens NY Stake |
| AmeriCorps St. Louis | MHH-Scotch Plains NJ Stake |
| Americorps VRC | MHH-Valley Forge PA Stake |
| Bergen County VOAD | MHH-Westchester NY Stake |
| Carolina Baptist Relief | MHH-Williamsport PA Stake |
| Catholic Charities, Diocese of Camden | MHH-Wilmington DE Stake |
| Christian Aid Ministries | MHH-York PA Stake |
| Convoy of Hope | MHH-Yorktown CT Stake |
| Durand Masonic Lodge | Nassau County Office of Emergency Management |
| Friends of Rockaway-World Bank | NECHAMA |
| GNJAC Methodist ERT | Never Alone, Never Afraid Inc. |
| GNJUMC – Methodist ERT | New York Cares |
| Habitat for Humanity of Bergen County | NJ 211 |
| Habitat for Humanity, Westchester County Chapter | NYAC United Methodist Church |
| Health and Welfare Council of Long Island | Oceanport NJ OEM |
| ICNA Relief | Poured-out |
| Inc. Village of Patchogue | Presbyter of Elizabeth Disaster Recovery Team |
| Islamic Relief USA | Rebuilding Together Bergen County |
| Jersey Cares | Rebuilding Together NYC |
| Lamb’s Chapel | Regional Catastrophic Planning Team |
| Lindy Manpower | Respond and Rebuild |
| Long Island Volunteer Center | Samaritan’s Purse |
| Lutheran Disaster Response | Sayville Chamber |
| Lutheran Social Ministries of NJ-Lutheran Disaster Response | Staten Island Council of Churches |
| Mastic Shirley COAD | Team Rubicon |
| Mennonite Disaster Service | Tennessee Baptist Disaster Relief |
| MHH-Brooklyn NY Stake | The Bonner Center |
| MHH-Buffalo NY Stake | The Salvation Army – Suffolk |
| MHH-Caldwell NJ Stake | UMCOR |
| MHH-Centreville VA Stake | United Methodist Church |
| MHH-Cherry Hill NJ Stake | United Way 2-1-1 Hudson Valley |
| MHH-Columbia MD Stake | United Way of Central Jersey |
| MHH-Dover DE Stake | United Way of Monmouth County |
| MHH-East Brunswick NJ Stake | United Way of Northern NJ |
| MHH-Frederick MD Stake | Virtua |
| MHH-Lynbrook NY District | Volunteer Army Foundation |
| MHH-Morristown NJ Stake | Washington State Conservation Corps |
| MHH-New Haven CT Stake | World Cares Center |
| MHH-New York NY Mission | World Renew Disaster Response |
| MHH-New York NY Stake | Zakat Foundation of America |
| MHH-Paterson NJ District |
FAQ
I’m in desperate need of volunteer programmers. I feel like I’ve been constructing an airplane while in freefall, writing the owners manual and giving hourly status reports for the last 1 1/2 months. We’re now gliding, but I need help building the rudder, landing gear, and gas gauges. Please comment below if you’re interested in helping out. Thanks!
Screenshots
A Christmas Vision: Dedicated to Emilie Parker
A Christmas Vision
Music and lyrics by Hayley Winslow. Adapted from a poem by Edgar Howard on the death of his young daughter.
![]() A Christmas Vision- Hayley Titus, Edgar Howard (MP3 Audio)
A Christmas Vision- Hayley Titus, Edgar Howard (MP3 Audio)
A Christmas Vision (Live Recording)
Perhaps this Christmas time is like all Christmas tides gone by.
Children’s faces are as bright with every sparkling eye.
Each face reflects a picture of a heart that throbs with cheer,
And yet it does not seem the same because she is not here.
The church choir sings the same Christ songs they’ve sung two-thousand years.
Priests and preachers tell God’s love ‘nor speak of hell or fear.
The wide world wears the same glad garb with Christmas joy and cheer,
And yet it does not seem the same because she is not here.
So few years she was my child; I held her in my arms.
Now I live without her and must hold her in my heart.
I yearn to find a sweet release at this joyous time of year,
But still my poor soul suffers, for I know she is not here.
Last night I saw a vision, of a child with laughing eyes,
and heard her speak a message from her place in Paradise,
And the message told me truly that one day I may share
A Christmas with the loved and lost- not here, but there.
My Great Great Grandfather, Edgar Howard lost his young daughter, Martha, at the age of 10. He wrote this poem which has been adapted and set to music by my sister, Hayley Winslow. On behalf of our family, we re-dedicate it to Emilie Parker, her family, and the families of all those who lost children and loved ones in Newtown, Connecticut.
Losing a child is undoubtedly one of the most devastating experiences a parent can face. That’s why it is imperative for parents to prioritize their children’s well-being, spending quality time with them and expressing love in various ways. While purchasing clothes from websites like Pastel Collections can be one way to show care, it is essential to remember that material possessions should not replace genuine affection and attention.
Edgar?s words helped heal my heart from the distance of a hundred years; I pray that his words and Hayley’s voice may heal many more hearts this Christmas.
A Christmas Vision.
Original Poem by Edgar Howard
Perhaps this Christmas-time is like all Christmas-tides gone by.
The children’s faces are as bright, and every sparkling eye
Reflects the picture of a heart that throbs with Christmas cheer,
And yet it does not seem the same, because–she is not here.
The church choirs sing the same Christ songs they’ve sung two thousand years,
And priests and preachers tell God’s love, nor speak of hell and fears.
The wide world wears the same glad garb with Christmas joy and cheer,
And yet it does not seem the same, because– she is not here.
Last night I saw a vision of a child with laughing eyes,
And heard her speak a message from her place in Paradise;
And the message told me truly that one day I may share
A Christmas-time with the loved and lost–not Here, but There.